On thirst August 2011, Mark Maunder had reveal, through a defacement experience, that “timthumb.php” script, included in hundreds of WordPress themes, was vulnerable to remote file inclusion (RFI) attack. TimThumb is small php script for cropping, zooming and resizing web images (jpg, png, gif).
The default configuration of “timthumb.php” script, in many WordPress themes, allow remote file inclusion from the following domains:
- flickr.com
- picasa.com
- blogger.com
- wordpress.com
- img.youtube.com
- upload.wikimedia.org
- photobucket.com
Unfortunately the domain code verification was buggy, allowing remote file inclusion if the above domain strings appears anywhere in the hostname, for example : picasa.com.zataz.com.
To create such DNS entries you need to have control on a zone hosted by a DNS server, the attack vector is more complex than a simple RFI attack how don’t need this kind of resource.
Since few weeks, I observe through my Honeynet that attempts to exploit this vulnerability are increasing and that it is now fully integrated as dork into the ByroeNet like tools. The fact is that more and more exploitable DNS entries are created how allow the TimThumb vulnerability exploitation.
For example, one of the most active TimThumb vulnerability domain is actually “picasa.com.xpl.be“, how has the following details :
- RFI IP : 98.158.186.250
- RFI FQDN : 90.158.186.250.static.midphase.com
- RFI Country : United States
Domain name servers authority for “picasa.com.xpl.be” and “xpl.be” domain names are :
; AUTHORITY SECTION:
xpl.be. 81644 IN NS ns2.afraid.org.
xpl.be. 81644 IN NS ns3.afraid.org.
xpl.be. 81644 IN NS ns1.afraid.org.
xpl.be. 81644 IN NS ns4.afraid.org.
;; ADDITIONAL SECTION:
ns1.afraid.org. 508 IN A 67.19.72.206
ns2.afraid.org. 206 IN A 174.37.196.55
ns3.afraid.org. 26 IN A 72.20.15.61
ns4.afraid.org. 26 IN A 174.128.246.102
afraid.org is a free DNS hosting, dynamic DNS hosting, static DNS hosting, subdomain and domain hosting services provider.
xpl.be domain name has been registered, the 5 April 2010, through Key-Systems GmbH a german domain name registrar and the registration informations are :
Registrant
Name : Dolores Aleman
Organisation : Dolores Aleman
Address : 1014 south 2nd st - 78550 Harlingen AL US
Email : [email protected]
Registrant technical contacts
Name : Mr XpL
Organisation : XpL inc
Address : 1014 south 2nd st - 78550 Harlingen AL US
Email : [email protected]
Both “picasa.com.xpl.be” and “xpl.be” are hosted on IP 98.158.186.250 from midPhase.com a hosting service provider, but this hosting service provider doesn’t provide any free hosting services. Also as you can see below the xpl.be web site designer know ASCII art.

Other example is “picasa.compress.cu.cc“, registered on “cu.cc” the 13 September 2011 by “[email protected]“. the domain name and website are hosted on 50Webs.com a free DNS and hosting provider.
“picasa.computergoogle.co.cc“, registered on “co.cc” registrar the 22 September 2011 by “[email protected]“. The domain name and website are hosted on 50Webs.com a free DNS and hosting provider.
“wordpress.com.daliacarella.com“, registered on “www.000domains.com” the 17 July 2011 by “[email protected]”. The domain name and the website are hosted on HostDime.com.
“blogger.com.donshieldphotography.com“, registered on Visual Solutions Group Inc the 19 January 2011 by “Don Shield Photography“. The domain name and the website are hosted on Visual Solutions Group Inc. “www.donshieldphotography.com” seem to be a legitimate Web site, but Visual Solutions Group Inc infrastructure seem also compromised.
“blogger.com.aptum.nu“, registered on nunames.nu the 24 October 2006 by “[email protected]”. The domain name and the website are hosted on ODERLAND. “aptum.nu” seem to be a legitimate Web site.
“blogger.com.jewelhost.co.uk” registered on 123-reg.co.uk the 04 May 2010 by “Callum Baillie”. The domain name and the website are hosted on JewelHost.co.uk a hosting provider how seem to be compromised.
“blogger.com.tara-baker.com” registered on Tucows Domains the 07 January 2010 by “UK2.net”. The domain name and the website are hosted on VC-Hosting.com a hosting provider how seem to be compromised.
“picasa.com.marcialia.com.br” has his domain name and website hosted on SERVER4YOU a hosting provider how propose free hosting trial during 6 months.marcialia.com.br seem to be a legitimate web site, the account seem to be compromised.
Other domains how are also participating to the TimThumb Botnet : “picasa.com.crimecyber.tk“, “blogger.com.1h.hu“, “picasa.com.nixonmu.com“, “blogger.com.lionsurveys.com“, “blogger.com.autoelectricahernandez.com“.
You have also “picasa.com.throngbook.com“, “blogger.com.cursos.secundariatecnica33.org” how are actually down.
All these compromised sites seem to be related to the Indonesian Byroe.net network.

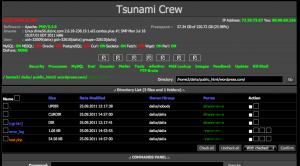
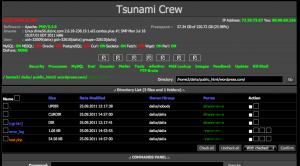
Here under you can find some live stats on the TimThumb vulnerability exploitation attempts detected by our Honeynet.