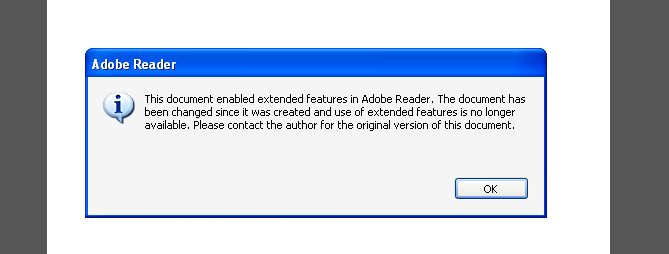
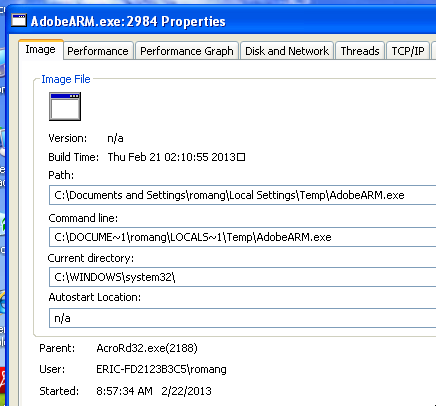
FireEye team has report a new Adobe Reader and Acrobat zero day exploited in the wild. This new 0day allow exploitation of the latest Adobe PDF Reader 9.5.3, 10.1.5, and 11.0.1 with sandbox bypass. In the information’s provided on FireEye blog post, it seem that two DLLs are dropped by the malicious PDF and that fake error message appears.
Adobe has acknowledge a potential vulnerability in his latest PDF Reader through a post on PSIRT (Product Security Incident Response Team) blog.
In the screenshot provided by FireEye, who don’t provide a lot of details, we can see a call to a “/index.php” page, which will potentially mean that the PDF 0day is streamed from the PHP file. Also we can observe that the involved user agent is MSIE 7 (aka Internet Explorer 7) under windows NT 5.1 (aka Windows XP).

According to a post on threatpost.com:
Attackers are using malicious PDFs posing as an application for an international travel visa to exploit a zero-day vulnerability in Adobe Reader and Acrobat.
Happy 0day Hunting
Despite the lack of information’s, after some researches yesterday night, I found the following file “Visaform Turkey.pdf” (f3b9663a01a73c5eca9d6b2a0519049e).
And through other researches, we found at 10pm the supposed C&C server aka “http://bolsilloner.es/index.php“.
“Visaform Turkey.pdf” was submitted on VirusTotal the 2013-02-11 and was recognized as “HEUR:Exploit.Script.Generic” at this time. This file was also submitted on malware tracker the 2013-02-12 and you can find some interesting information in this submission. Also the same file was submitted the 2013-02-13 to Wepawet. C&C server was submitted to jsunpack the 2013-02-13 without any associate outputs.
Adobe Security Advisory APSA13-02
Adobe PSIRT has release a security advisory APSA13-02 regarding two vulnerabilities CVE-2013-0640 (base CVSS score of 9.3) and CVE-2013-0641 (base CVSS score of 9.3) in Adobe Reader and Acrobat XI (11.0.01 and earlier), X (10.1.5 and earlier) and 9.5.3 and earlier for Windows and Macintosh. Also this security advisory confirm the exploitation of these vulnerabilities in targeted attacks through spear phishing campaign. Adobe is working on the issue and will provide updated versions asap. Affected softwares are:
- Adobe Reader XI (11.0.01 and earlier) for Windows and Macintosh
- Adobe Reader X (10.1.5 and earlier) for Windows and Macintosh
- Adobe Reader 9.5.3 and earlier 9.x versions for Windows, Macintosh and Linux
- Adobe Acrobat XI (11.0.01 and earlier) for Windows and Macintosh
- Adobe Acrobat X (10.1.5 and earlier) for Windows and Macintosh
- Adobe Acrobat 9.5.3 and earlier 9.x versions for Windows and Macintosh
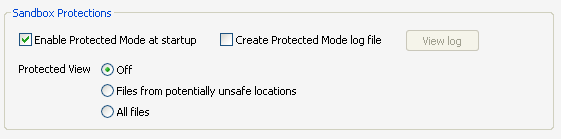
Regarding Adobe security advisory, the vendor recommend, for users of Adobe Reader XI and Acrobat XI for Windows, as workaround to enable “Protected View“. To enable this setting, choose the “Files from potentially unsafe locations” option under the Edit > Preferences > Security (Enhanced) menu. The problem is that despite “Protected Mode” is activated, and as discussed on Twitter with @artem_i_baranov, and also mentioned by Ars Technica, “Protected View” is off when using the default version.
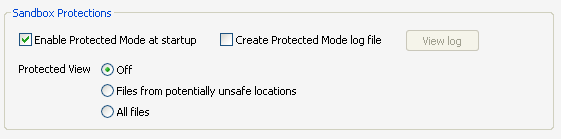
According to the documentation of “Protected View“:
When Protected View in enabled, PDFs are displayed in a restricted environment called a sandbox.
So it means, that by default sandbox is deactivated during display of PDFs.
Also Mac OS X users, and Linux users are not protected by this workaround who is only available for Windows.
Vendors Informations
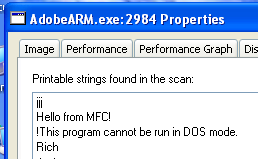
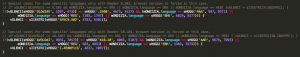
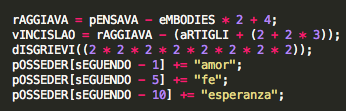
FireEye has release new details regarding the payload used by the vulnerabilities. Also they point the fact on the high usage of Italian in the JavaScript embedded in the malicious PDF file.
Sophos has release a screenshot of the “Visaform Turkey.pdf” file and additional informations.

“Visaform Turkey.pdf” Sample Analysis
Based on the poor sample we found on malware tracker (please re-enable the download functionality !), we started to analyse it.
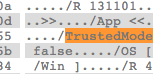
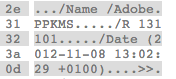
First interesting information: It could be that the “Protected Mode” could be bypassed via pdf properties. After some researches it doesn’t seem linked.
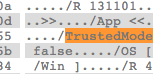
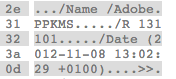
Second interesting information: The date in the document appear to be f****ng old !!!! (2012-11-08).
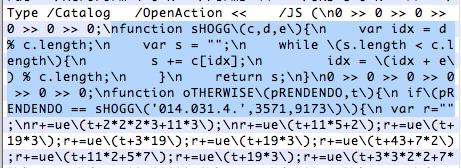
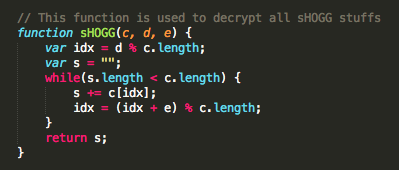
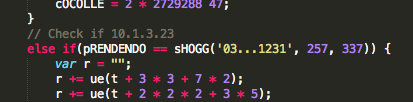
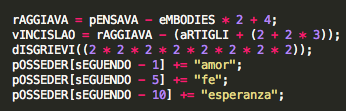
Third sHOGG function is used to decrypt a bunch of variables in the code.
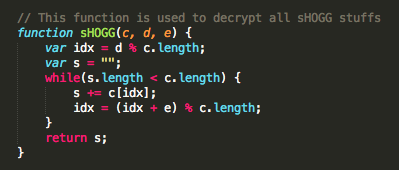
By using this function on certain variables, we can confirm that the following Adobe Readers were targeted:
- 10.0.1.434
- 10.1.0.534
- 10.1.2.45
- 10.1.3.23
- 10.1.4.38
- 10.1.4.38ARA
- 10.1.5.33
- 11.0.0.379
- 11.0.1.36
- 9.5.0.270
- 9.5.2.0
- 9.5.3.305
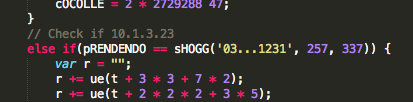
Also some special cases, for some specific languages and only with Reader 9.502 or 10.104, are forced.
I also can confirm that the code is heavily obfuscated with bunch of variable and functions names in Italian, like “dIAVOLO”, “bENEDETTO”, “sENTIRSI”, “aPPARENZA”, “fISAMENTE”, “pRESUNSI”, “cOCOLLE”, “sCHIUMA”, “pENITENZA”, etc.
Regarding different sources, files dropped by the PDF:
- “L2P.T” (3a2547af14b5621f43481a70f32ccef3). Analysis on VirusTotal.
- “LangBar32.dll” (97777F269AE807891DAC4B388C66A952). Analysis on VirusTotal.
- “Visaform Turkey.pdf” (F475A43D374334197099ADA17720EB00). Analysis on VirusTotal.
- “D.T” (CB33E97F46A219804DDB373FF982D694). Analysis on VirusTotal.
As @binjo has released the code of Adobe Javascript, I also release my studies on it.
I will keep you in touch, in this post, if I have any additional information’s.