During some investigations, associated to a packed version of the September Internet Explorer CVE-2012-4969 vulnerability, I found an unknown exploit targeting Microsoft Internet Explorer. The code was found on CLEAN MX and the evidences was dated of 2011-10-25.
After some researches on Internet, I found a blog post “Internet Explorer Option Element Remote Code Execution” from Ivan Fratric related to CVE-2011-1996 who has similar familiarities with the founded code. Ivan spoke about an PoC but never delivered it.
In Internet Explorer, the implementation of Select HTML element contains an array of pointers to the Option elements the Select element contains. This array is called the Option cache. Normally, whenever an Option element inside a Select element is accessed via JavaScript, Option cache is rebuilt, thus ensuring its consistency. However, there are some JavaScript methods that can be used to delete and modify the Option elements contained inside the Select element without rebuilding the Option cache. In combination, these methods enable modifying a previously deleted Option element.
If you remember CVE-2011-1996 was patched in MS11-081 the 11 October 2011 and details on the vulnerability were provided by Ivan Fratic the 12 October 2011. This vulnerability is affecting Microsoft Internet Explorer 6,7 and 8. So less than 12 days after the release of the Microsoft patch, an exploit was found gathered on Clean MX…
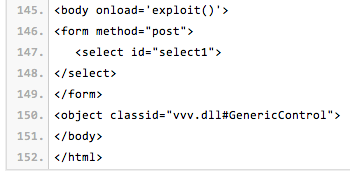
Regarding Clean MX, this exploit was found used in the wild on “hxxp://hb7.in/n/vvv.html“. And the “hb7.in” domain name was previously found on MALWARE.pl and on jsunpack the 24th October.
Now since the 9 January, this exploit is now integrated into Metasploit framework as “ms11_081_option” targeting Internet Explorer 8 on Windows XP, Vista and 7. Just enjoy 🙂