In my previous blog post, I have detail how to install ArcSight Logger L750MB (the 49$ one) on a Centos 5.x. In this post I will explain you how to install a Windows Syslog ArcSight Connector, how to collect Windows events with Snare and how to push all these events to your Logger.
ArcSight Logger L750MB – network flows
As described in my “ArcSight Logger L750MB features and limits” blog post, this product version of ArcSight Logger has some limitations.
10 devices maximum could send they logs to the L750MB Logger. A device is the IP of the event generator. For example, you could have a Linux RHEL 5 server with Snort, the 2 products will be considered coming from the same source IP. Also, a device on the Logger, is a combination of a event source IP and a “Receiver“. We recommend you to use the same “Receiver” for common products on the same source IP.
With the L750MB version you will be allowed to install SmartConnectors to support these products :
- Cisco PIX/ASA
- Cisco IOS Routers and Switches
- Juniper Network and Security Manager (NSM)
- Juniper JUNOS Routers and Switches
- Red Hat Enterprise Linux
- SNARE
- Snort
They are 2 provided SmartConnectors in ArcSight Download Center, one to install a Syslog server under Windows, and the other one to install a Syslog server under Linux. All the supported products should send they’re logs to the SmartConnector in Syslog 514/UDP or 514/TCP. When the products logs are received by the ArcSight SmartConnector, these logs are normalized in CEF (Common Event Format) and send encrypted to the Logger in SmartMessage format on port 9000/TCP. ArcSight SmartConnector is not only normalizing logs in CEF, but we will not explain in this blog post all the SmartConnectors capabilities. Here under a small representation of the network flows.
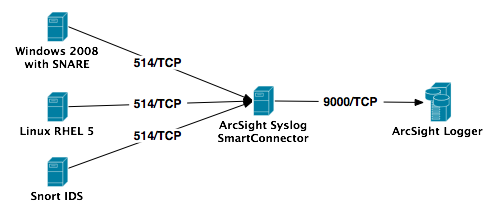
As you know, UDP is not a protocol what we can trust for delivering informations. UDP does not provide guarantee of delivery which can cause data to go missing. When considering connection problems or missing data, the TCP connection is much more desirable. Also, if you need to encrypt the data connection, you should use TCP. So we strongly recommend you to communicate with the ArcSight Syslog SmartConnector in TCP protocol. But the free version of Snare for Windows only support UDP protocol, so we will do this demonstration with UDP. If you want to have TCP support for Snare, you need to buy Snare server.
ArcSight Logger L750MB – Receiver configuration
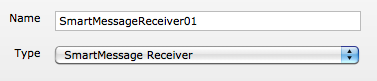
First of all we need to create a “Receiver” on the Logger. This “Receiver” will be a SmartMessage one, in order to have the possibility to receive events in CEF.
To do this configuration, you only need to identify you on your Logger and to go in the “Configuration” menu, then click on the “Event Input/Output” sub-menu. The receiver will listen on port 9000/TCP, same port as for the Logger Web interface. We will name the receiver “SmartMessageReceiver01“, his type will be “SmartMessage Receiver” and his encoding “UTF8“.
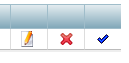
Once saved, you will find your configured receiver in the “Receivers” list. On the right of the receiver, in the receiver list, you need to active it by clicking on extreme right icon. When the receiver will be actif the extreme right icon will be replaced by the following one.
 We will not pre-configure the devices, cause they will be auto-discovered by the Logger. And we will also not pre-configure a “Devices Group” and a “Storage Rule“.
We will not pre-configure the devices, cause they will be auto-discovered by the Logger. And we will also not pre-configure a “Devices Group” and a “Storage Rule“.
ArcSight Syslog SmartConnector installation
Now we will install the Syslog SmartConnector on a dedicated box in order to centralize the communication from all the devices and to the Logger. The Syslog SmartConnector will use the TCP protocol. In our example, we will install the Windows Syslog SmartConnector (ArcSight-5.0.2.5703.0-Connector-Downloadable-Logger-Win.exe).
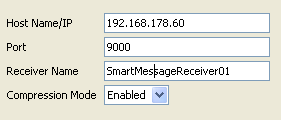
Execute the installation executable, and choose a proper installation folder, we recommend you to not install the SmartConnector on the C drive. Then choose a typical install and the installation executable will install the software and launch the SmartConnector wizard. Choose “ArcSight Logger SmartMessage (encrypted)” as destination and provide all the required informations for the SmartConnector and Logger interconnexion. The “Receiver Name” should be the same as declared on the Logger, here “SmartMessageReceiver01“.
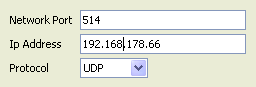
The next screen will indicate you that a Syslog SmartConnector will be installed, and you will have to configure the syslog server by providing the listener IP address (here 192.168.178.66) and the related protocol (here UDP).
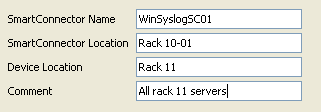
Now give a name (here WinSyslogSC01), a SmartConnector location (here Rack 10-01), a device location (here Rack 11) and a comment (here All rack 11 servers). These informations are optionals.
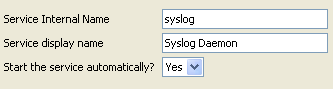
You will see in the last screen, that it is possible to reconfigure the SmartConnector with the “bin/runagentsetup.bat” script. Choose now if you want to install the SmartConnector as a standalone application or as a service, and if the service should start automatically.
The Syslog SmartConnector installation is now finished, but don’t forget to start the Syslog SmartConnector service 🙂
Snare Event Log Agent for Windows installation
Download Snare Event Log Agent for Windows and install it one every Windows server or station you want, but don’t forget that you are limited to 10 devices maximum.
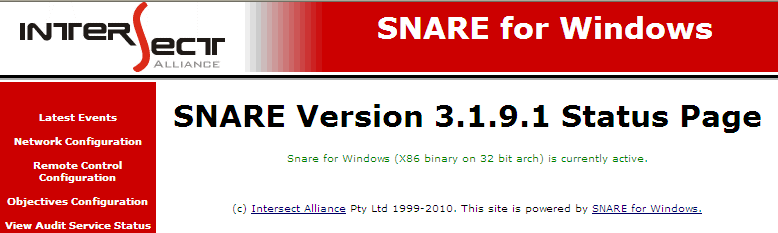
Execute the installation binary, accept the agreement, choose an installation folder, let Snare to take over control of the EventLog configuration, enable the Snare remote control interface with a password and finish Snare installation. Launch “Snare for Windows” from you “Program” menu, you will be connected in the web remote control interface on port 6161/TCP.
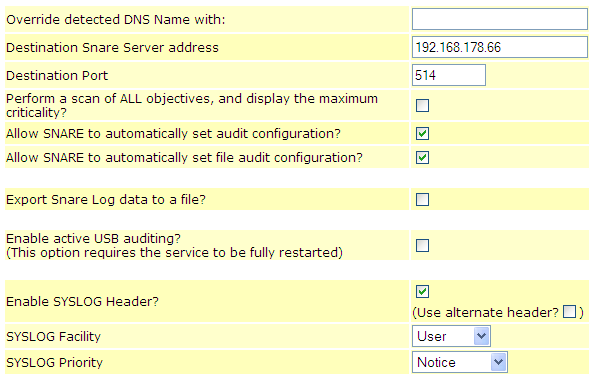
In the “Network Configuration” menu, configure the “Destination Snare Server” (here 192.168.178.66), the “Destination Port” (here 514), and click the checkbox for “Enable SYSLOG Header“, the save the configuration.
To reload the Snare configuration just click on the “Reload Settings” in the “Apply the Latest Audit Configuration“. And here we go, the Windows events are send to the Logger. For further instructions on how to configure Snare we recommend you to read the Snare documentation 🙂
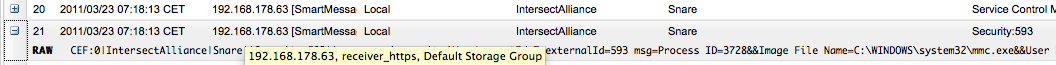
Windows Events in your Logger
In ArcSight Logger you will now have all the Windows Events directly accessible by the “Analyze” menu and “Search” sub-menu.
Hello,
I have one problem. I installed and configured all things by your instruction. All device’s time zones are same. But on the Arcsight Logger Server, only connector logs collected. Real client’s(Windows8) log transferred to Smart Connector. But on the Logger Server my Win8 client doesn’t appearing. Please help me?
Hi,
Please can i correct you, Intersect Alliance the authors of Snare do not require you to buy the Snare server to gain TCP support. Snare enterprise agents provide TCP support and Snare enterprise agents can be deployed without the Snare server and happily work with other servers such as Arcsight with TCP Protocol. That said Snare enterprise agents is the licenced version available from Intersect Alliance.
Regards
Intersect Alliance
Thanks for the article, very helpful.
I’ve a Logger (appliance one) and I can’t have it recognizing Windows 2008 logs sent through Snare. Any idea?
You mentioned “If you want to have TCP support for Snare, you need to buy Snare server”.
The Snare Server with the Snare Enterprise Agents provides TCP and interoperability with ArcSight, though the Snare Enterprise Agents by themselves support TCP and can be configured to send to any port – or multiple ports. The Snare Enterprise Agents can be purchased from Intersect Alliance.
I’m surprised they wouldn’t include a windows connector. I would think that they’d know you could use such a snare workaround; so I wonder why they would limit that.
Hi
In my configuration the logger never opens port 9000 after I configure the receiver and enable it.
I have the test proposal license.
Tks
Nuno
the above example is good for only the windows…
what about the configuration for Router and Switch?….Please explain with example.
Hello vetrivijay,
I’m actually working on new tutorials with Cisco network devices. Stay tuned.
Regards