FireEye (@fireeye) were the first to speak around the Oracle Java 0day in a nice blog post “Zero-Day Season is Not Over Yet“. As they mentioned in the blog post it was just a matter of time that a PoC will be released. The tweet was dated from 9:26 PM – 26 August, 2012.
https://twitter.com/FireEye/status/239806161874993152
@jduck member of Metasploit team had sufficient information’s contained in this blog post to seek the mentioned infected domain “ok.xx4.net“, how was hosted in China with “59.xxx.xxx.62” IP address and running on “IceWarp/4.1” web server port 80/TCP or 443/TCP. A scan of around 20K servers and the juicy “applet.jar” was found 🙂 Less than 5 hours (2:01 AM – 27 August, 12) later a PoC was available, and less 24 hours later (11:36 AM – 27 August, 2012) the fully functional exploit was added to Metasploit. This exploit is working on Microsoft Windows with Internet Explorer, Firefox & Chrome, but also under Linux with Firefox running the latest version of Java SE 7.0.
https://twitter.com/_juan_vazquez_/status/240020063460143104
Lot of medias, antivirus companies have then try to sold us that this 0day was found in a “targeted” attack, you known the APT stuff.
etc.
But just a moment, why should all new discovered 0day be a part of a “targeted” attacks ? Just do some researches on the Oracle Java 0day origin.
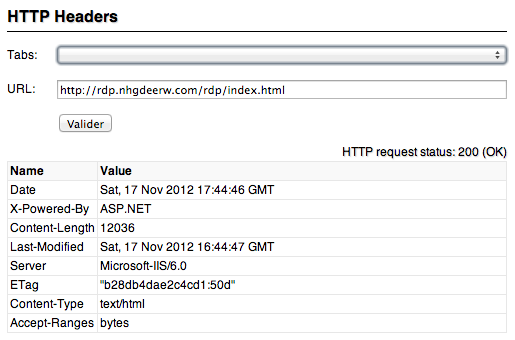
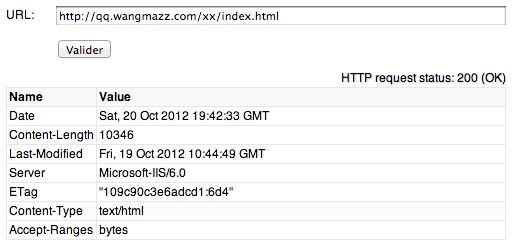
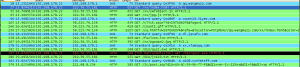
The infected web server is “ok.aa24.net” with “59.120.154.62” IP address. If you take a look on robtex, you can see that the domain name is hosted by afraid.org, a free DNS hoster, involved in many past attacks. First fact, why a “targeted” attack will use a well-known domain name malware hoster ?
The IP address is hosting other domain names and this IP is also known as malware spreader since May 2012 (check SCUMWARE.ORG for all results for 59.120.154.62). Second fact, why a “targeted” attack will use a will know IP address as source of the attack ? You know that all security vendors are selling “reputation” blacklists stuff ?
If you take a look at all the results of SCUMWARE.ORG you can see well-known Trojan and downloaders (Trojan.Win32.Agent.srjf, Win32/Agent.PBJ trojan, Win32/Spindest.A trojan), etc. Third fact, why a “targeted” attack will use so bad malwares to infect a “targeted” target 🙂
Now we will take a look at the source code of “/meeting/index.html” page. Ok, ok, I admit the page is containing an obfuscated JavaScript 🙂 Then just deobfuscate this JavaScript (My pastebin deobfuscated code). We can find some interesting patterns in the JavaScript code like “xiaomaolv“, “woyouyizhixiaomaolv” and “conglaiyebuqi“. All these patterns are Mandarin and Putonghua transliterated pronunciation.
- woyouyizhixiaomaolv – ??????? – I have a small donkey
- conglaiyebuqi – ????? – Never played
If you do a simple search on Google, you will find that these stuff were presented at BlackHat USA 2010 in “Balancing the Pwn Trade Deficit“. So these patterns are known since 2 years minimum. Fourth fact, why a “targeted” attack will use known patterns, aren’t anti viruses only good to detect static patterns ? Also guys, not everything how is coming from China is a part of a big conspiracy against the world.
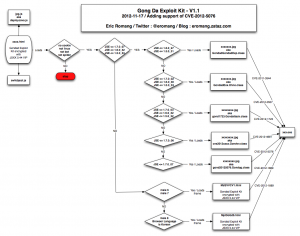
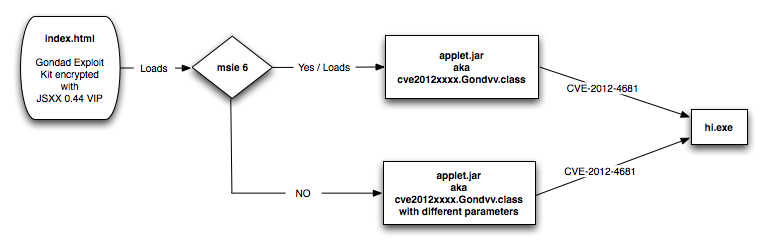
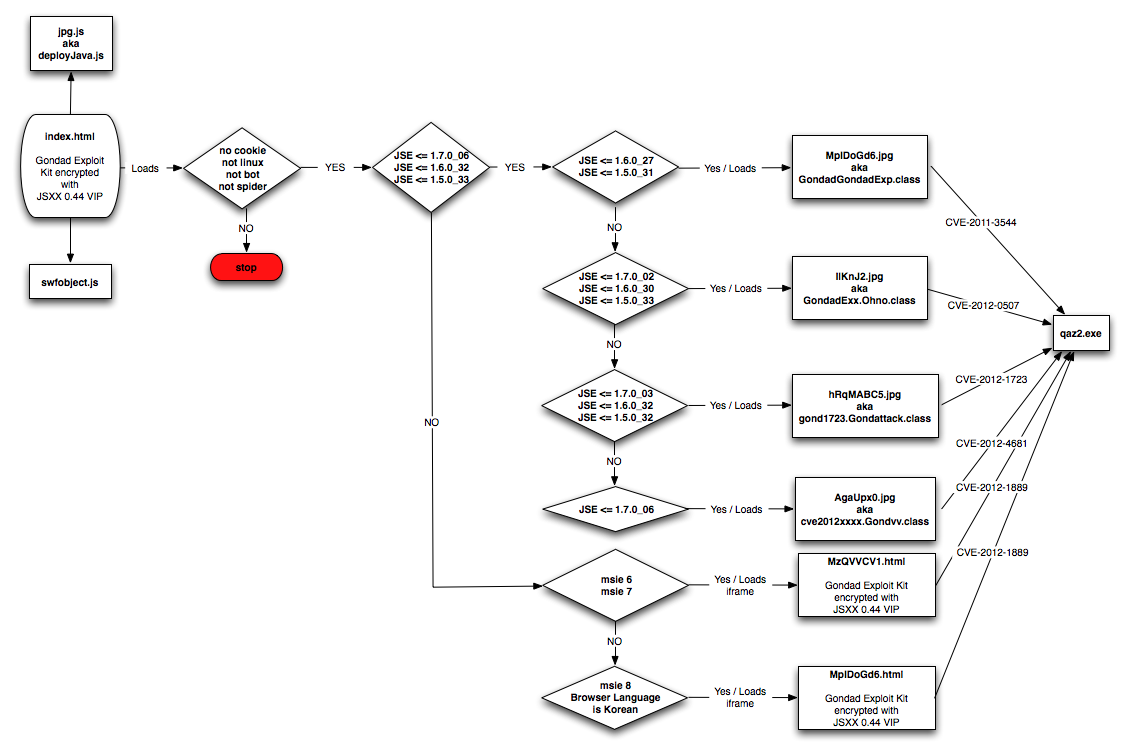
Ok, let continue to analyze the deobfuscated JavaScript code. We can find other interesting patterns like “Gondvv.class“, “gondady” and “gondad“. Here also a simple search on Google and you will find that this code is part a well-known exploit kit, “Gondad Exploit Kit“. Fifth fact, is a “targeted” attack using popular exploit kits ?
Now we will continue with the “hi.exe” file, located in “/meeting/hi.exe” folder. Through malwr.com malware service analysis, you can see that the malware is requesting for “hello.icon.pk” domain name, how is hosted on IP 223.25.233.244 located in Singapore. This malware is catched by 30 of 41 anti viruses on VirusTotal and the domain name is also hosted on afraid.org …. Still a “targeted” attack ?
Just a moment, shouldn’t we not try to download other potential malware hosted on this server ? For example “antivirus.exe“, “officeupdate.exe” and “upgrade.exe” discovered with SCUMWARE.ORG. All these malwares are still available on the infected server and are all detected by a minimum of 25 VirusTotal anti viruses. Still a “targeted” attack ?
Also, what is surprising is that the infected server is still online, shouldn’t a server involved in a “targeted” attack been shutdown by they’re sponsors if they are catched (remember Stuxnet, Flame, etc.) ?
Should I continue with the C&C server how is also known since some months ? I think I will stop here.
What I think, is that cve2012xxxx.Gondvv.class exploit is unique, that the time frame between the discovery and the weaponization of the 0day is also unique. But what I really don’t believe is that this 0day was used in targeted attacks…
More references on the doubt of this “targeted” attack:
Trend Micro – Java Runtime Environment 1.7 Zero-Day Exploit Delivers Backdoor
While some reports have gone on to say that this particular zero-day exploit might be used in targeted attacks, our analysis showed that this may not be the case. The sites where the exploit is hosted are known distributors of various malware. The server that BKDR_POISON.BLW connects to is also a known C&C used by malware. Targeted attacks are known to stay under the radar to successfully operate. The domains/IPs this attack use alone say that there was no intention of staying hidden.