You maybe remind end of August Java 0day, aka CVE-2012-4681. This 0day was found in an html page containing obfuscated JavaScript. The obfuscation was made by a tool initially called “Dadong’s JS Obfuscator“.
/*Encrypt By Dadong’s JSXX 0.44 VIP*/
This obfuscator was used, in the Java 0day case, to hide the presence of Chinese Gong Da Pack (aka Gondad).
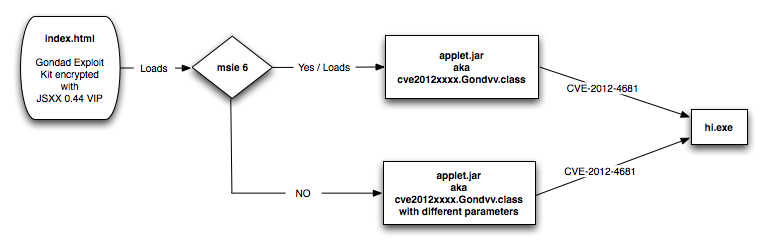
The August version of Gong Da Pack was exploiting CVE-2012-4681 regarding the following diagram, but previous studies, in March, have reveal that this Pack was also dealing with CVE-2011-2140 (Adobe Flash Player), CVE-2012-0003 (Windows Multimedia Library) and CVE-2011-3544 (Oracle Java Rhino exploit).
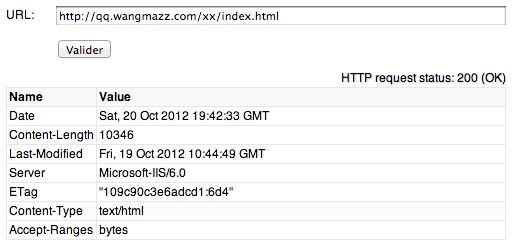
A new version of Gong Da Pack is emerging, and is getting more complex. This version was discovered on “hxxp://qq.wangmazz.com/xx/index.html” a web site how is actually no more accessible.
“qq.wangmazz.com” was hosted on 210.56.55.106, AS38197, in Hong Kong and “wangmazz.com” domain name was created the 2012-10-19, through name.com registrar, for “jie jiu ([email protected])“.
The “index.html” file was containing JavaScript code obfuscated by the same obfuscator as for the Java 0day, but with a different name. I think we could simply rename “Dadong’s JS Obfuscator” to “JSXX VIP JS Obfuscator“. It seem that “Dadong’s” or “xx.xiamaqq.com” are the name of the campaigns. “index.html” file was recognized only by 9 on 44 anti-viruses on VirusTotal.com.
/*Encrypt By xx.xiamaqq.com’s JSXX 0.44 VIP*/
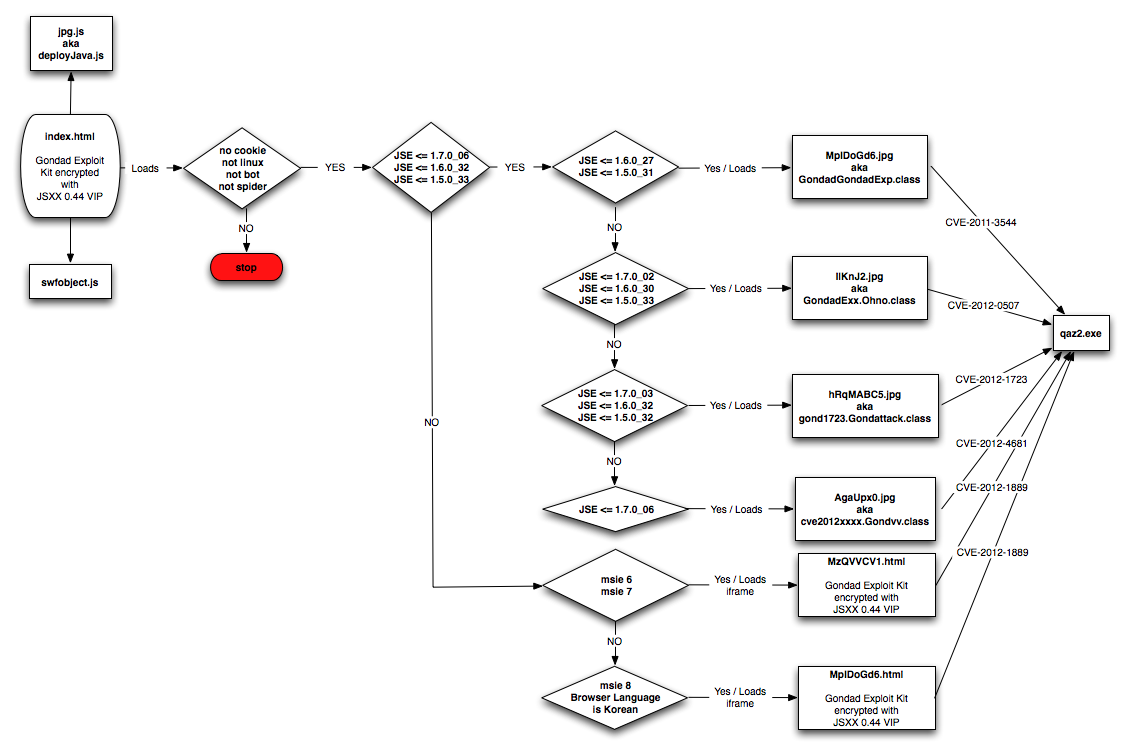
After de-obfuscation of the “index.html” file you can see that Gong Da Pack has involve to the following diagram.
Gong Da Pack is still dealing with CVE-2011-3544 (Oracle Java Rhino exploit) and CVE-2012-4681 (Oracle Java August 0day), has add CVE-2012-0507 (another Oracle Java exploit), CVE-2012-1723 (another Oracle Java exploit) and CVE-2012-1889 (Microsoft XML Core Services), but has removed CVE-2011-2140 (Adobe Flash Player) and CVE-2012-0003 (Windows Multimedia Library) for this campaign.
An interesting part discovered in the code is that the bad guys were trying to target Internet Explorer browsers with korean language support for CVE-2012-1889.
Here under some information s regarding the different files:
- MpIDoGd6.jpg (a406045e5ade95b93eb1796e473dc879) : 6/43 on VirusTotal.com
- IlKnJ2.jpg (491a5a6a0df358272650a0c324ca179e) : 10/44 on VirusTotal.com
- hRqMABC5.jpg (b55e122428f44b244fa8bf1452c2bfa4) : 20/44 on VirusTotal.com
- AgaUpx0.jpg (a810b99c42491f264da76fd13e4ebccd) : 27/43 on VirusTotal.com
- MzQVVCV1.html (d6a6dea31a7239729f364afba206abfd) : 9/44 on VirusTotal.com
- MpIDoGd6.html (a5408a47201bfcaaf5506a6974b464e5) : 7/44 on VirusTotal.com
“qaz2.exe” PE32 executable is recognized as a trojan by 23/44 anti-viruses targeting online gamers. This file is downloaded from “xx.xiamaqq.com“, located on 210.56.55.161, , AS38197, in Hong Kong. “xiamaqq.com” domain name was also created the 2012-10-19, through name.com registrar, for “jie jiu ([email protected])“.
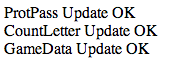
After installed “qaz2.exe” is connecting to “o108.cvnieksff.com” on 111.68.8.254, in Hong Kong. “cvnieksff.com” domain name was created the 2012-05-11, through enom.com registrar, for “Yu Yuming ([email protected])“. The first connection is HTTP GET method to “/jc/post.asp?d10=MACADDRESS&d11=ver-jc-119xx&d21=56&d22=OSTYPE“. Response to this method is:
In conclusion, Gong Da Pack (aka Gondad) seem to continue to target asian countries, and has involve in order to mostly use latest Oracle Java exploits. As you can see this campaign has target online gamers, what is steal not clear is when and how the August Java 0day has been pushed into Gong Da Pack.
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
Gondad Exploit Pack Evolutions http://t.co/ZEdSGUbF
RT @unixfreaxjp: #Malware Info – Gong Da/Gondad Exploit Pack Evolutions – http://t.co/3AzBCwoP < Nice research! Should write EK more, Eric:) rgds!: @eromang
RT @unixfreaxjp: #Malware Info – Gong Da/Gondad Exploit Pack Evolutions – http://t.co/3AzBCwoP < Nice research! Should write EK more, Eric:) rgds!: @eromang
#Malware Info – Gong Da/Gondad Exploit Pack Evolutions – http://t.co/3AzBCwoP < Nice research! Should write EK more, Eric:) rgds!: @eromang
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
Gong Da / Gondad Exploit Pack Evolutions http://t.co/zV3SXwuW #exploit
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
RT @Dinosn: Gong Da / Gondad Exploit Pack Evolutions http://t.co/0WRcJJJr
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
Gong Da / Gondad Exploit Pack Evolutions http://t.co/Jh4tQRh2 >>> very nice write up, thank you for sharing!
RT @Dinosn: Gong Da / Gondad Exploit Pack Evolutions http://t.co/0WRcJJJr
Security researcher @eromang performed an analysis of the Gong Da (or Gondad) trojan http://t.co/DColCU6w
RT @Dinosn: Gong Da / Gondad Exploit Pack Evolutions http://t.co/0WRcJJJr
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
Gong Da / Gondad Exploit Pack Evolutions => http://t.co/VHKZ5eNu
Gong Da / Gondad Exploit Pack Evolutions http://t.co/0WRcJJJr
RT @unpacker: [EricRomang] Gong Da / Gondad Exploit Pack Evolutions http://t.co/zB2JKyI9
RT @unpacker: [EricRomang] Gong Da / Gondad Exploit Pack Evolutions http://t.co/NDrxEyX2 #fb
[EricRomang] Gong Da / Gondad Exploit Pack Evolutions http://t.co/zB2JKyI9
RT @ChadChoron: RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/bINBY6lN #infosec #zataz
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/xWr0uhIm #infosec #zataz
RT @eromang: Gong Da / Gondad Pack Evolutions. Exploit pack involved in CVE-2012-4681 discovery http://t.co/bINBY6lN #infosec #zataz