In a previous post, we have seen that Joomla wgPicasa component LFI exploit was more used than other LFI exploits. I was interested to see if the source IPs of this particular LFI attack was implicated into other attacks and integrated into bigger botnets.
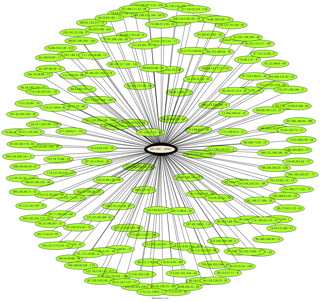
First of all, since the 15 April 2010, we have 165 different unique source IPs how have attempt to use the Joomla wgPicasa component LFI exploit on our HoneyNet. These source IPs have generate 20 351 events. Here under an afterglow representation of all these IPs with they weight in term of events.
Are these source IPs involved in other activities ? Surely yes 🙂 After some crazy SQL queries on our HoneyNet database, we got these results.
- 45 others exploits where detected from the same source IPs who are exploiting the Joomla wgPicasa component LFI vulnerability.
- Some of these 45 exploits are targeting others LFI exploits, for examples :
- Joomla Component com_ccnewsletter controller
- Ideal MooFAQ Joomla Component file_includer.php
- rgboard _footer.php skin_path parameter
- phpSkelSite TplSuffix parameter
- MODx CMS snippet.reflect.php reflect_base
- TBmnetCMS index.php content Parameter
- etc.
- Some of these 45 exploits are targeting RFI exploits, for examples :
- ProdLer prodler.class.php sPath Parameter
- Datalife Engine api.class.php dle_config_api Parameter
- SERWeb main_prepend.php functionsdir Parameter
- Possible AIOCP cp_html2xhtmlbasic.php
- Mambo/Joomla! com_koesubmit Component ‘koesubmit.php’
- eFront database.php
- etc.
- Some of these 45 exploits are trying SQL injection, for examples :
- MYSQL SELECT CONCAT SQL Injection
- SQL Injection Attempt UNION SELECT
- SQL Injection Attempt SELECT FROM
Here under an afterglow representation of the interactions between all source IPs and them attached exploits attempts.
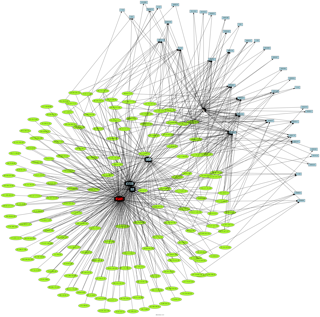
We can clearly see that most of these source IPs are controlled by Remote File Inclusion botnets, but some of them are standalone and only exploiting the particular Joomla wgPicasa component LFI.