Microsoft has release, the 10 July 2012, during his July Patch Tuesday, two security advisories and nine security bulletins. On the two security advisories one is preventing a future 0day disclosure and on the nine security bulletins six of them are fixing publicly disclosed vulnerabilities.
Microsoft Security Advisory 2719662
MSA-2719662 recommend to disable as soon as possible Windows Sidebar and Gadgets available on Windows Vista and Windows 7. Possible execution of arbitrary code could be exploited through Windows Sidebar when running insecure Gadgets. KB-2719662 Fix IT solution will provide you a way to disable Windows Sidebar and Gadgets. Microsoft thanks Mickey Shkatov and Toby Kohlenberg for this MSA.
It is quiet surprising and disturbing that Microsoft recommend to disable Windows Sidebar and Gadgets how are used by a bunch of end users. The argument used to push the user to deactivate these stuffs is that Windows 8 will depreciate Sidebar and Gadgets. Why disable features from a supported version because the new version will no more use these features. You can compare this deactivation as disabling Widgets under Mac OS X. I think that the reason is quiet simple, Mickey Shkatov will present, at Black Hat US 2012 the 26 July, a session called “We have you by the Gadgets“. And I feel that the discovered vulnerabilities are quiet to long and hard to fix, and that Microsoft has decide to no more support Sidebar and Gadgets.
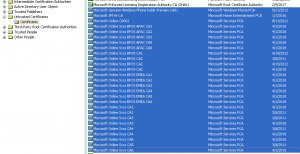
Microsoft Security Advisory 2728973
MSA-2728973 is the suite of the Flame malware attacks consequences, more Microsoft digital certificates have been moved to the “Untrusted Certificates Store”. The main reasons is that Microsoft is considering that the affected digital certificates are outside his secure storage practice, and that the RSA keys length are less than 2048 bits, how is considered as a best practice. KB-2728973 will correct these issues. Just remember that in Jun 2012 Microsoft had decide to block RSA keys that were under 1024 bits.
What is interesting is that these keys were considered not following Microsoft secure storage practice. Were these keys accessed by unnecessary custodians ? Were the keys not stored in an encrypted format or the key-encrypting keys not stored separately from data-encrypting keys ? Were the keys storage locations stored in multiple uncontrolled locations and forms ? Were the keys distributed in an insecure manner ? No answers 🙂
MS12-043 – Microsoft XML Core Services
MS12-043 security update, classified as Critical, allowing remote code execution, is the fix for CVE-2012-1889 found exploited in the wild in Jun 2012. This vulnerability was demonstrated by a Metasploit PoC the 15 Jun and then integrated into Blackhole exploit kit at the end of Jun.
MS12-044 – Cumulative Security Update for Internet Explorer
MS12-044 security update, classified as Critical, allowing remote code execution, is fixing two vulnerabilities CVE-2012-1522 and CVE-2012-1524. Both vulnerabilities were reported through VeriSign iDefense Labs coordinated vulnerability disclosure. CVE-2012-1522 was discovered by Jose A. Vazquez and CVE-2012-1524 discovered by Omair.
MS12-045 – Microsoft Data Access Components [MDAC]
MS12-045 security update, classified as Critical, allowing remote code execution, is fixing one vulnerability CVE-2012-1891. This vulnerability was reported through ZDI coordinated vulnerability disclosure.
MS12-046 – Visual Basic
MS12-046 security update, classified as Important, allowing remote code execution, is fixing one vulnerability CVE-2012-1854. This vulnerability has been discovered exploited in the wild since Mid-March ! The targeted attacks were focusing on Japanese organizations.
MS12-047 – Windows Kernel-Mode Drivers
MS12-047 security update, classified as Important, allowing escalation of privilege, is fixing two vulnerabilities CVE-2012-1890 and CVE-2012-1893. CVE-2012-1890 has been publicly disclosed and discovered by Nicolas Economou of Core Security Technologies and Qihoo 360 Security Center. CVE-2012-1893 was reported through Lufeng Li of Neusoft Corporation coordinated vulnerability disclosure. CVE-2012-1893 has a public exploit code but limited to local DoS. Some details of CVE-2012-1890 have been provided by Core Security Technologies.
MS12-048 – Windows Shell
MS12-048 security update, classified as Important, allowing remote code execution, is fixing one vulnerability CVE-2012-0175. This vulnerability was reported through Adi Cohen of IBM Security Systems coordinated vulnerability disclosure. Vulnerability details have been provided by Adi Cohen of IBM Security Systems.
MS12-049 – TLS
MS12-049 security update, classified as Important, allowing information disclosure, is fixing one vulnerability CVE-2012-1870. This vulnerability has been publicly disclosed.
MS12-050 – SharePoint
MS12-050 security update, classified as Important, allowing escalation of privilege, is fixing 6 vulnerabilities CVE-2012-1858, CVE-2012-1859, CVE-2012-1860, CVE-2012-1861, CVE-2012-1862 and CVE-2012-1863.
CVE-2012-1858 has been publicly disclosed by Adi Cohen of IBM Security Systems and could allow XSS attacks. A proof of concept code is available on IBM Security Systems.
CVE-2012-1859, CVE-2012-1860, CVE-2012-1861, CVE-2012-1862 and CVE-2012-1863 were reported through coordinated vulnerability disclosure.
MS12-051 – Microsoft Office for Mac
MS12-051 security update, classified as Important, allowing escalation of privilege, is fixing one vulnerability CVE-2012-1894. This vulnerability has been discovered exploited in the wild during targeted attacks against Tibet organizations.