Oracle was under pressure since 26 August, release date of technical information’s and exploit code of the Oracle Java 0day consisting in two highly critical vulnerabilities.
Four days later Oracle has release an out-of-band security patch Java SE versions 7u7 (1.7.0_07) and 6u35 (1.6.0_35).
This out-of-band update correct 4 vulnerabilities, 3 of the 4 vulnerabilities have a base CVSS score of 10.0.
CVE-2012-4681, with a CVSS base score of 10.0, is one of the well known vulnerabilities of Java 7 0day and has been discovered by Adam Gowdiak of Security Explorations in April 2012. This vulnerability was affecting Java 7 Update 6 and before.
CVE-2012-1682, with a CVSS base score of 10.0. This vulnerability was affecting Java 7 Update 6 and before.
CVE-2012-3136, with a CVSS base score of 10.0. This vulnerability was affecting Java 7 Update 6 and before.
CVE-2012-0547, with a CVSS base score of 0.0. This vulnerability was affecting Java 7 Update 6 and before, Java 6 Update 34 and before.
But regarding Security Explorations they are still around 26 reported vulnerabilities how are open and with unknown impact.
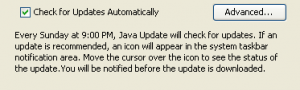
By default installed Java is configured on automatic update notification, but this process is also configured by default to be activate only every Sunday at 9:00 PM. This elapse time will provide more times to bad guys…We highly recommend you to update asap your Java installation !
But unfortunately the new update Java 7 Update 7 contain a critical flaw, discovered 24 hours by Security Explorations after the release of the patch. This new discovered security flaw allows an attacker to bypass the Java security sandbox completely, making it possible to install malware or execute malicious code on affected systems. No details are actually public and no known exploit of the new flaw has yet been found in the wild. We could hope that this new security flaw will not be discovered by bad guys and that Oracle will patch them during his next release plan, the October 16.


1 thought on “CVE-2012-4681 Vulnerability Patched in Out-of-Band Oracle Java Update”
Comments are closed.